Biomedical research is inherently collaborative — data flows between academic institutions, pharmaceutical companies, and healthcare systems, each with its own cloud infrastructure. To enable this work, platforms must meet researchers where they are.
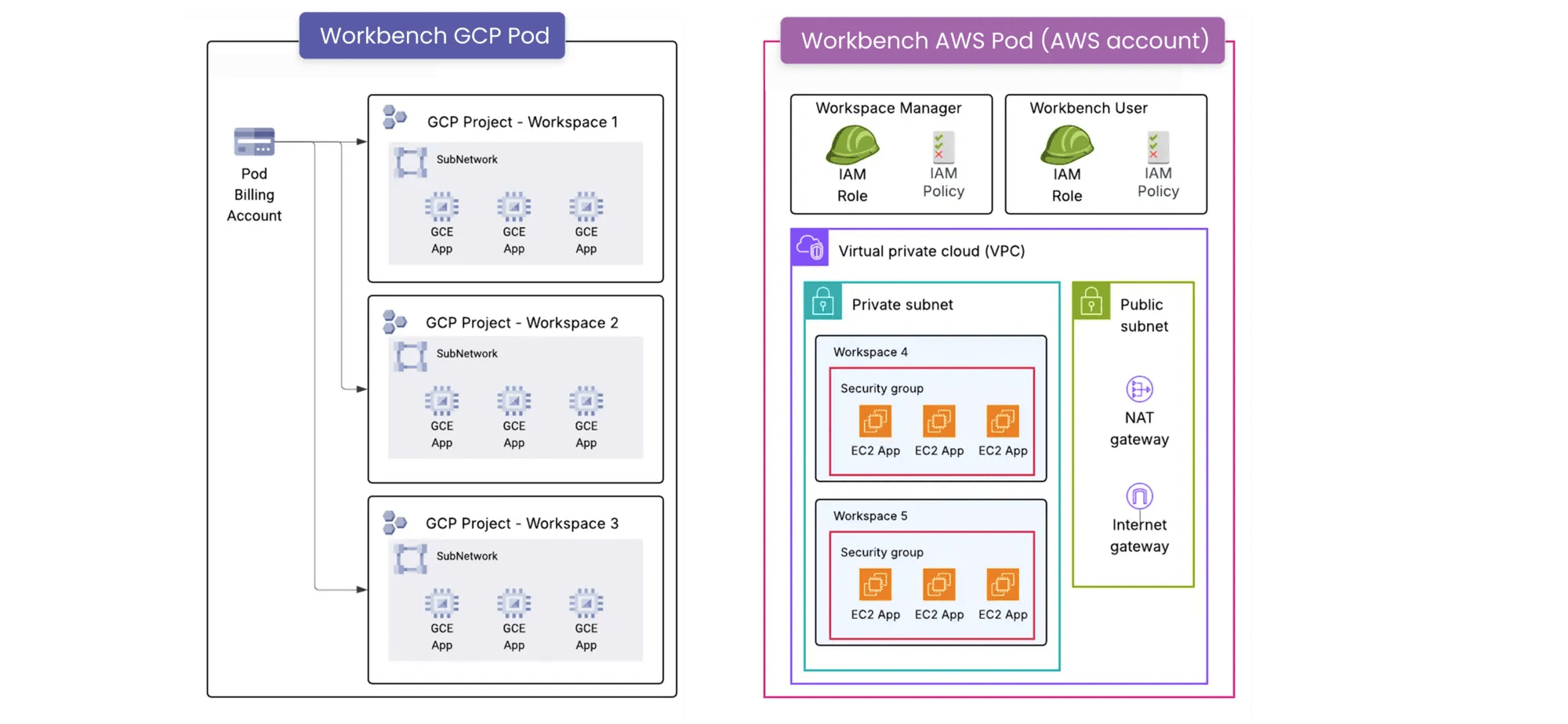
Verily Workbench, built on Pre, has historically leveraged the native architecture of Google Cloud Platform (GCP). Many research teams have infrastructure investments in other cloud providers. To reach a wider audience, we’ve evolved Workbench to support AWS.
Today, we explore the engineering philosophy and technical architecture behind our latest milestone: support for Amazon Web Services (AWS) within Workbench. Researchers can now use Workbench’s governance, analysis, and collaboration capabilities with AWS infrastructure and specialized services.
This architecture required reimagining how we handle identity and isolation. We’ve outlined the core concepts below. Full engineering specifications, including our multicloud resource model and the 'cloud sync' mechanisms for IAM, are detailed in our technical deep dive whitepaper.